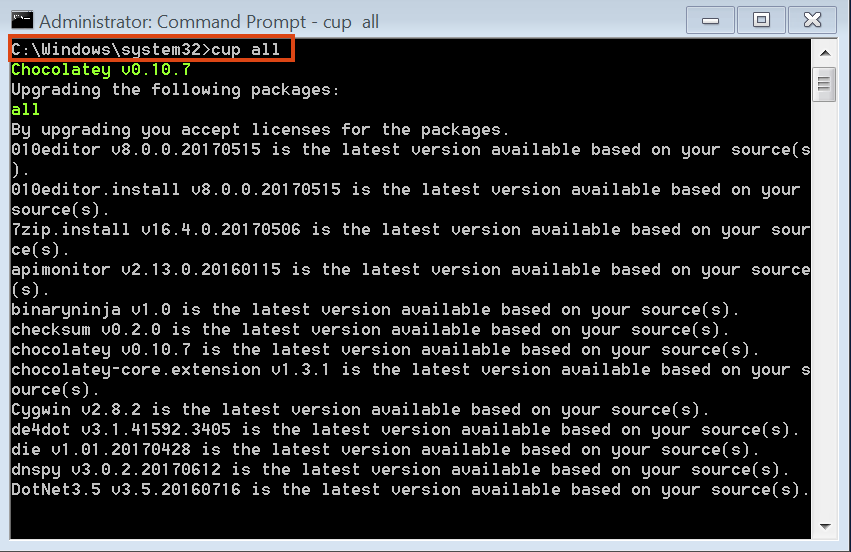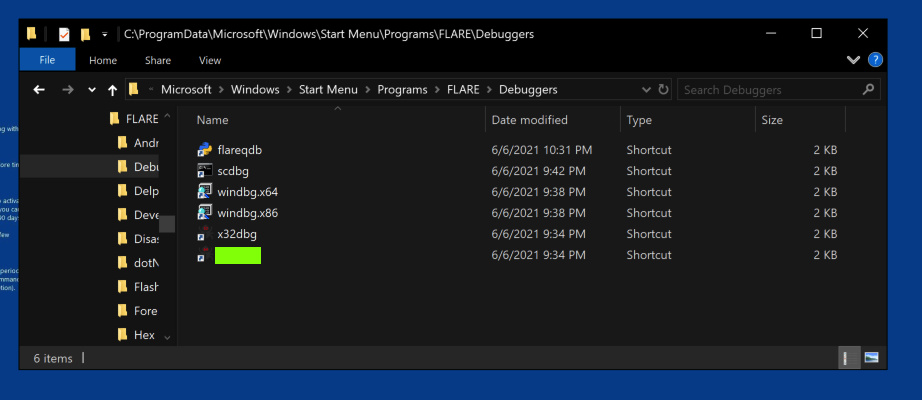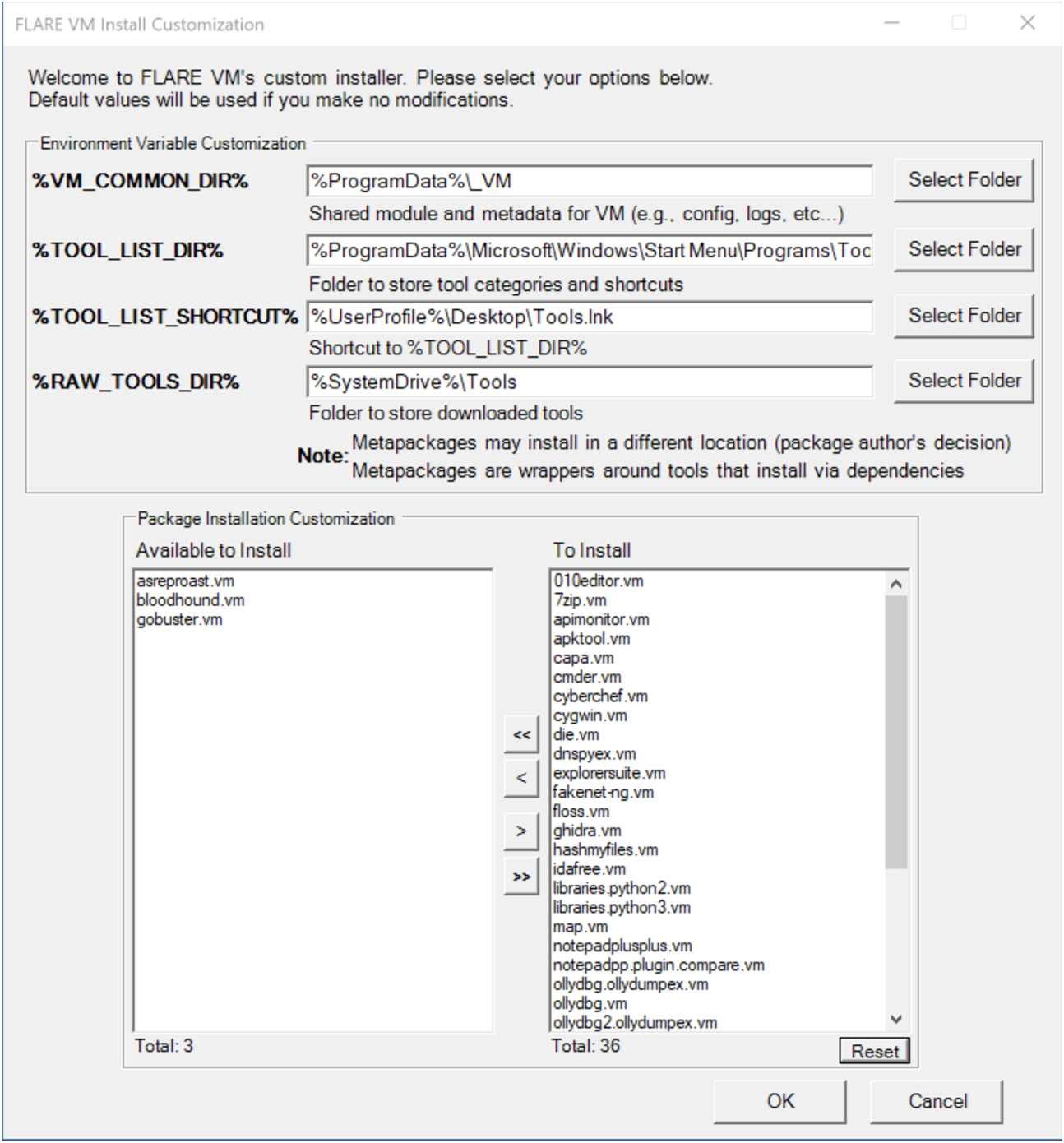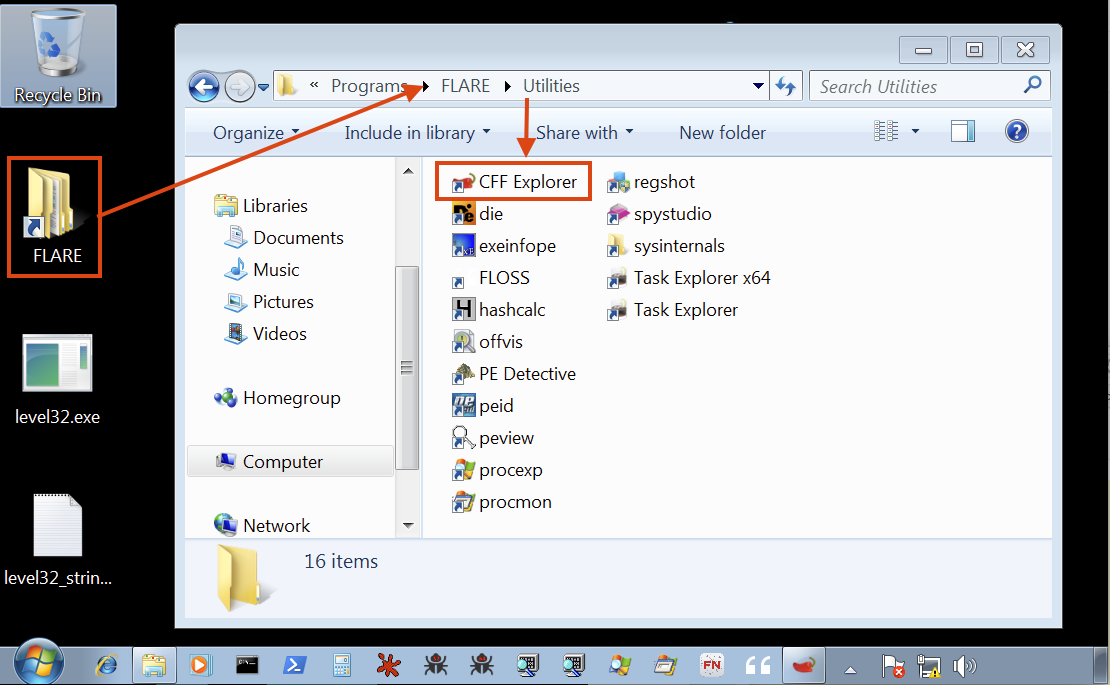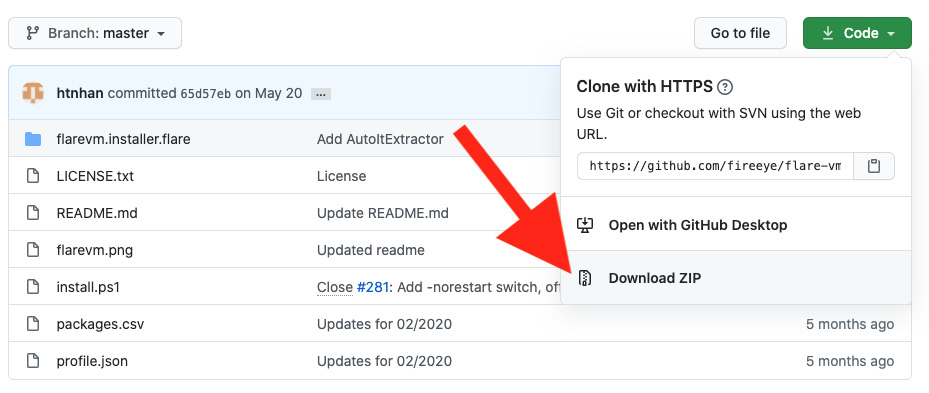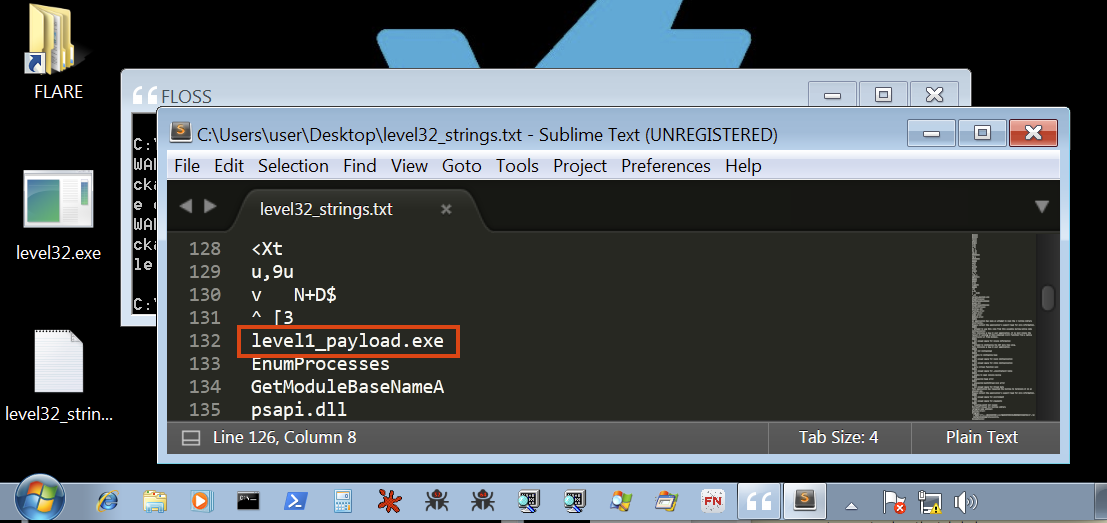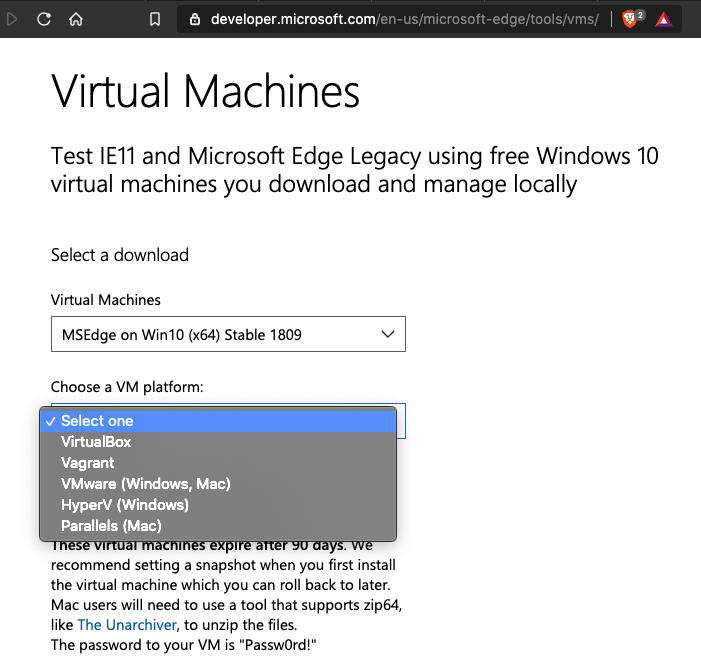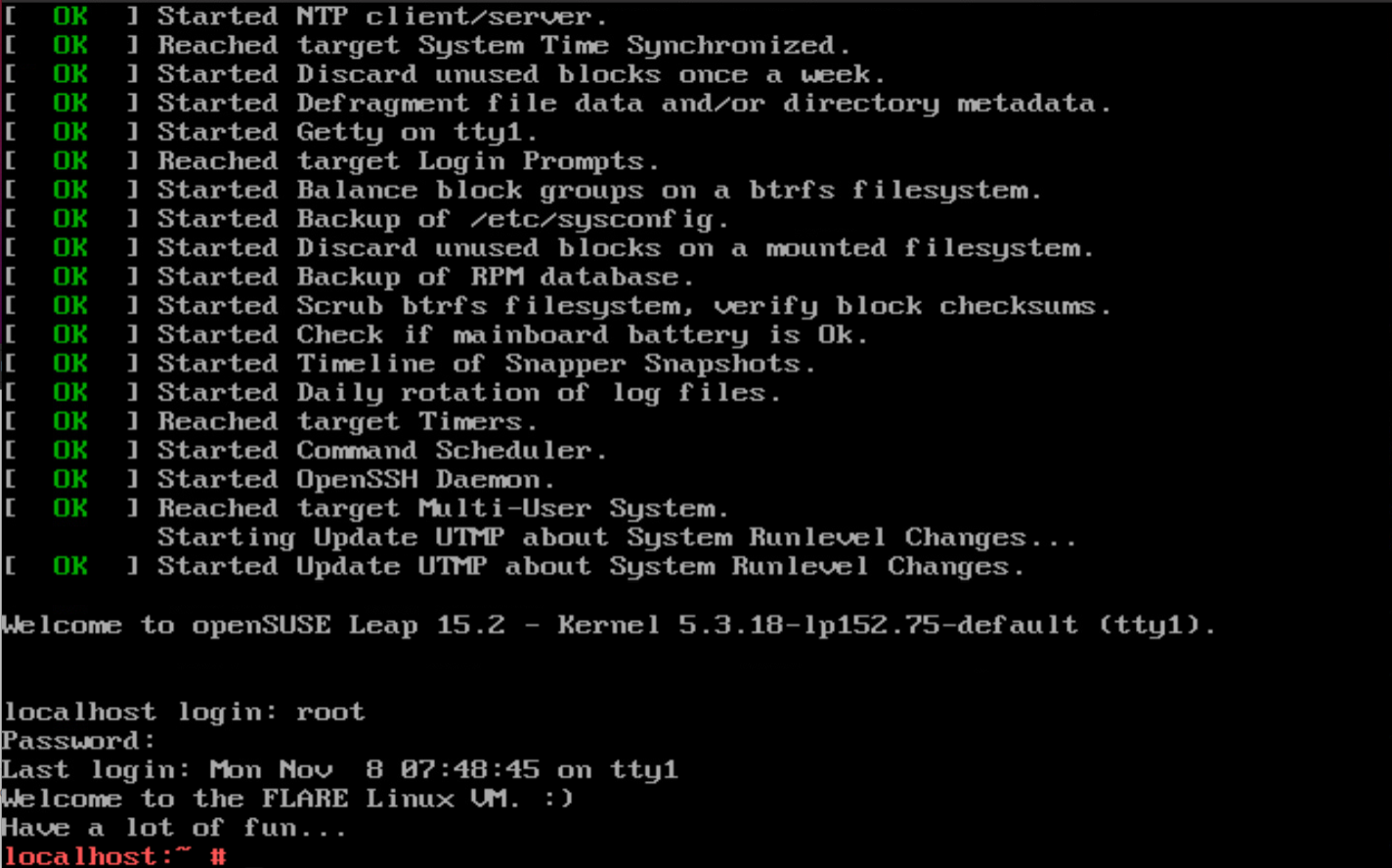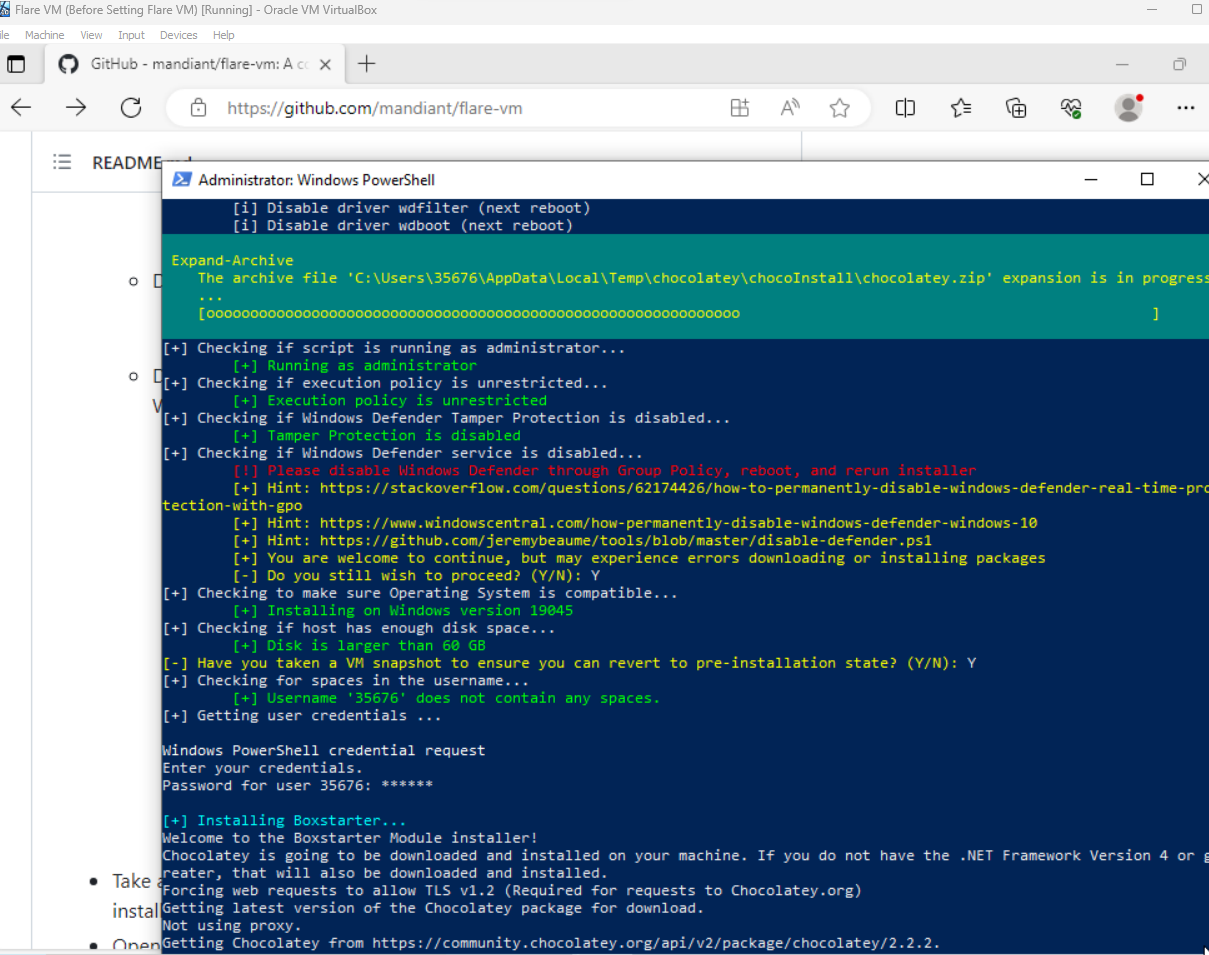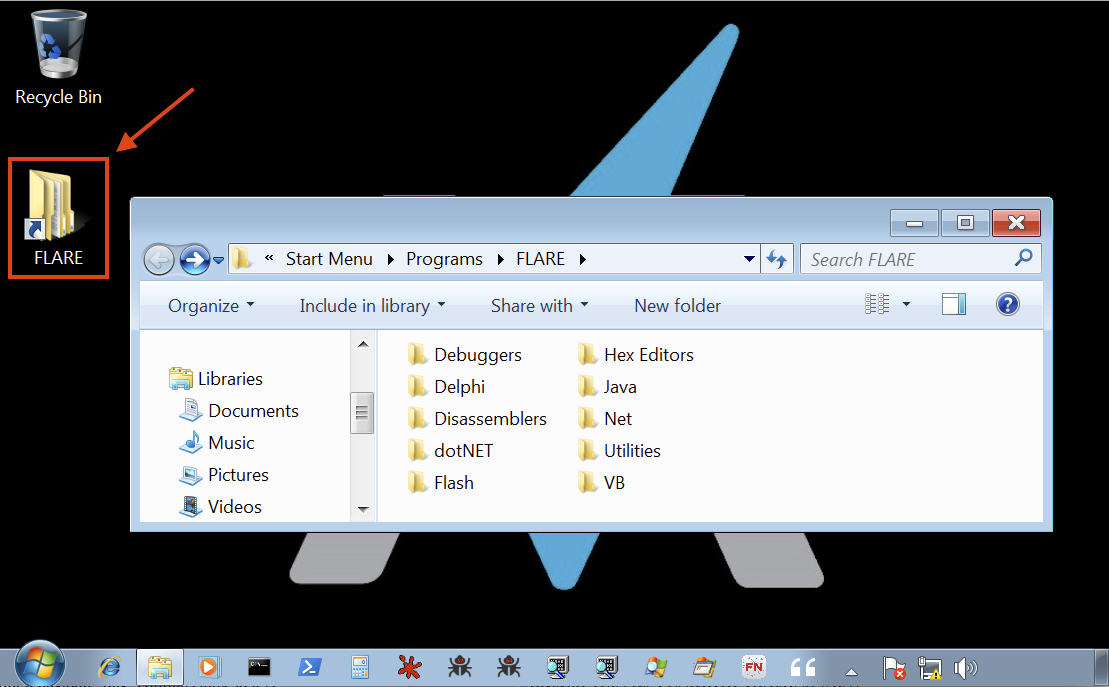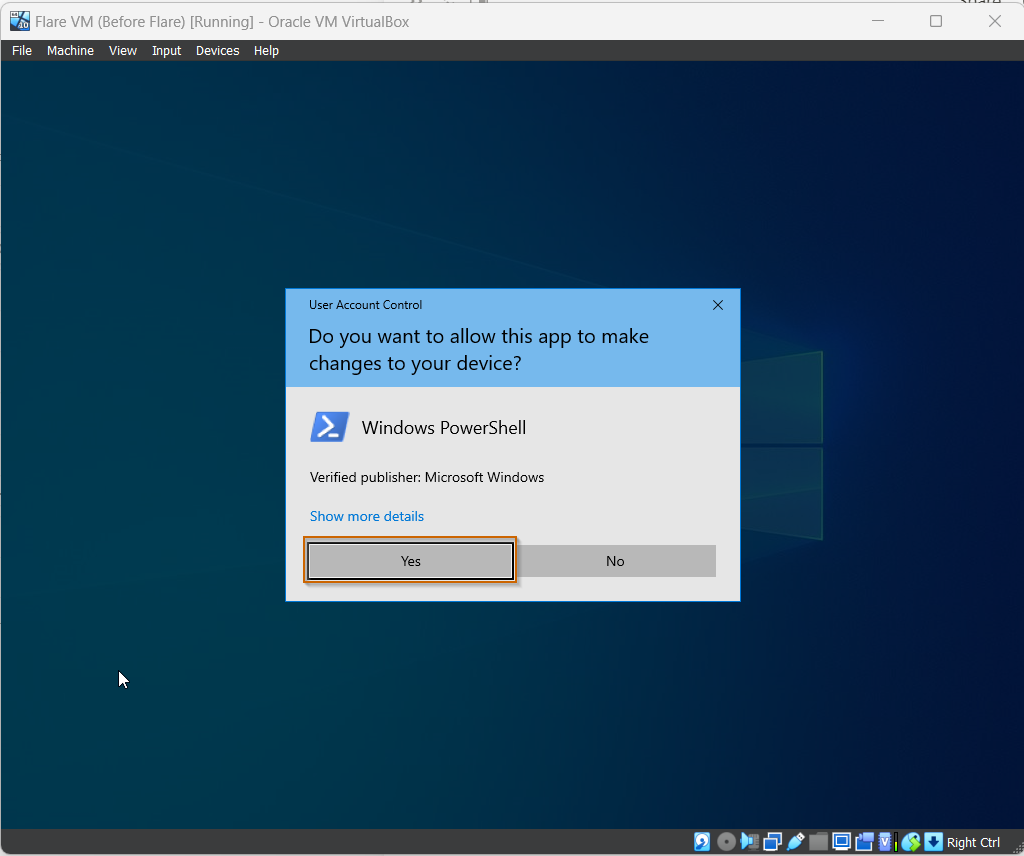
How to deploy Flare VM. A Practical walk through for Setting up… | by ฿Ʉ฿฿Ɏ Ⱨ₳ӾⱫ | Martian Defense Cybersecurity

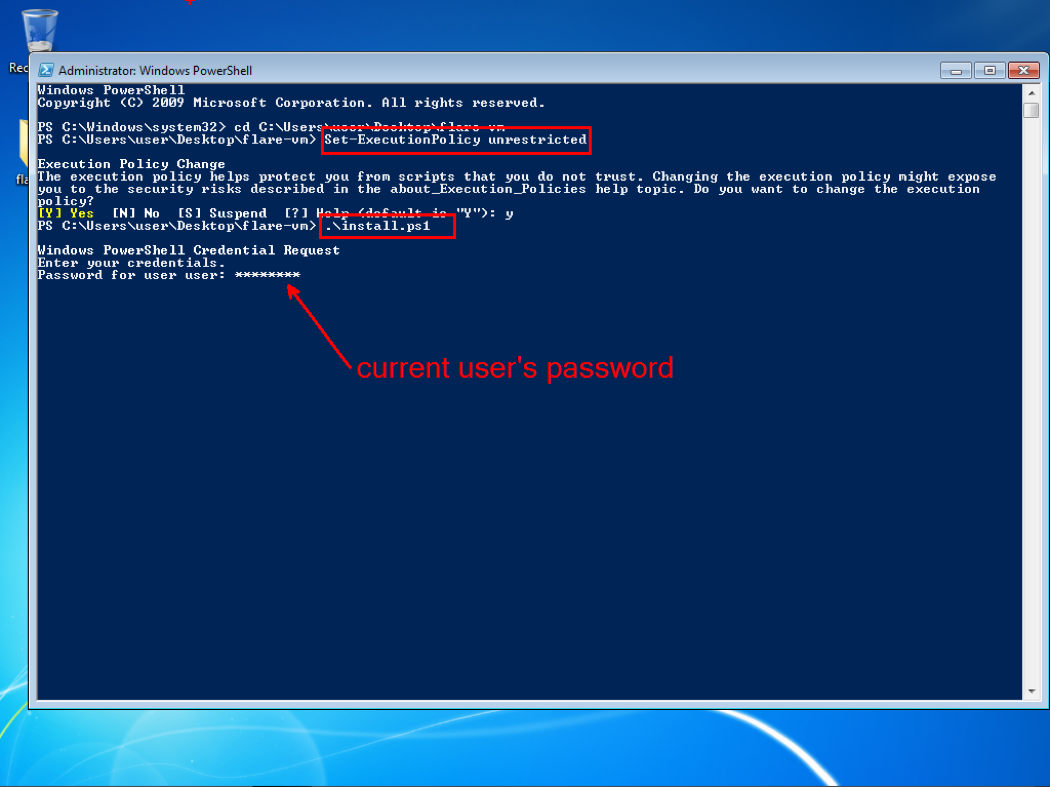
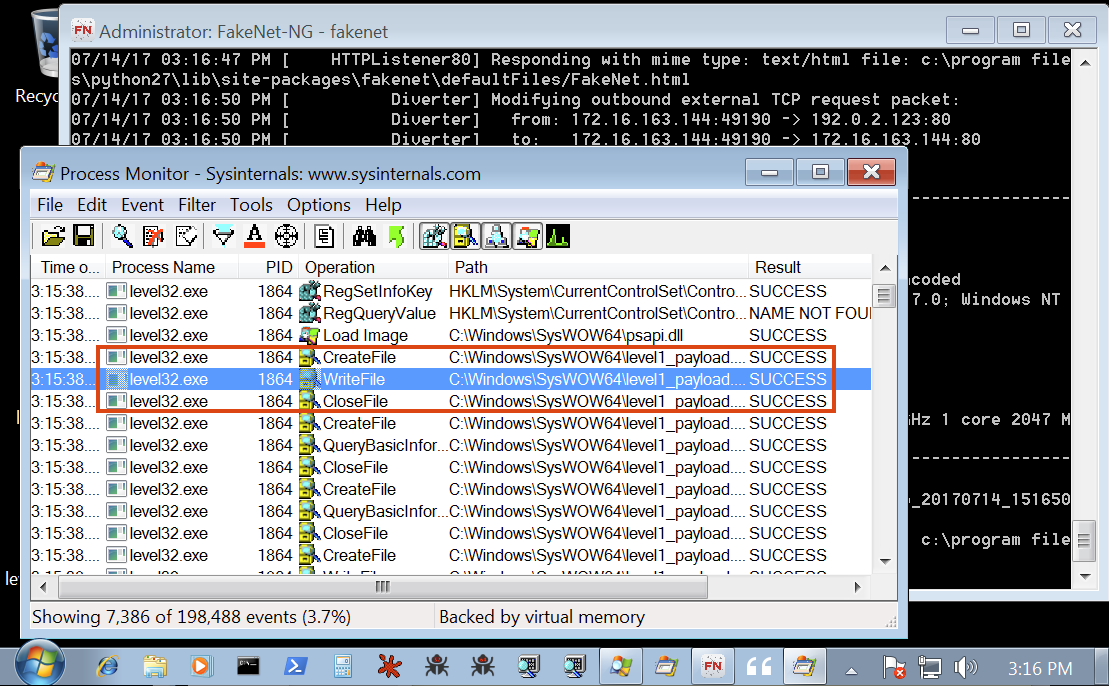
Building A Secure Malware Analysis Lab From Scratch- A Step-by-Step Guide | by Indranil | System Weakness

Flare-VM Sandbox Guide: Creating an Isolated Lab Environment for Malware Analysis & Reverse Engineering | by Muhammad Haroon | Medium